从零搭建自己的SpringBoot后台框架(十三)
Hello大家好,本章我们添加防止XSS攻击功能 。有问题可以联系我mr_beany@163.com。另求各路大神指点,感谢
一:什么是XSS
XSS攻击全称跨站脚本攻击,是一种在web应用中的计算机安全漏洞,它允许恶意web用户将代码植入到提供给其它用户使用的页面中。
你可以自己做个简单尝试:
1. 在任何一个表单内,你输入一段简单的js代码: <script>for(var i=0;i<1000;i++){alert("弹死你"+i);}</script> ,将其存入数据库;
2. 在页面上一个div元素内直接展示第一步内存入的值,你会发现弹出框出现了;
以上两个示例仅仅算是恶作剧,恶意用户能做的更多,如获取用户信息,进行“网络钓鱼”攻击等。
应对XSS攻击的其中一个方式就是后端对输入内容进行过滤,输入内容里面的敏感信息直接过滤,如 <script> 标签等。
二:添加Jsoup依赖
Jsoup使用标签白名单的机制用来进行防止XSS攻击, 假设白名单中只允许p标签存在, 此时在一段HTML代码中, 只能存在p标签 , 其他标签将会被清除只保留被标签所包裹的内容,当然,Jsoup不仅仅可以用来过滤,还可以用来爬虫,这里先不做说明,后期会单写一篇文章进行讲解。
<dependency> <groupId>org.jsoup</groupId> <artifactId>jsoup</artifactId> <version>1.10.2</version> </dependency>
三:创建过滤器
在core下创建 filter 文件夹
1、创建过滤规则
package com.example.demo.core.filter;
import org.jsoup.Jsoup;
import org.jsoup.nodes.Document;
import org.jsoup.safety.Whitelist;
/**
* @author 张瑶
* @Description: xss非法标签过滤
* @date 2018/5/16 20:03
*/
public class XssFilterUtil {
/**
* 使用自带的basicWithImages 白名单
* 允许的便签有a,b,blockquote,br,cite,code,dd,dl,dt,em,i,li,ol,p,pre,q,small,span,
* strike,strong,sub,sup,u,ul,img
* 以及a标签的href,img标签的src,align,alt,height,width,title属性
*/
private static final Whitelist whitelist = Whitelist.basicWithImages();
/** 配置过滤化参数,不对代码进行格式化 */
private static final Document.OutputSettings outputSettings = new Document.OutputSettings().prettyPrint(false);
static {
// 富文本编辑时一些样式是使用style来进行实现的
// 比如红色字体 style="color:red;"
// 所以需要给所有标签添加style属性
whitelist.addAttributes(":all", "style");
}
public static String clean(String content) {
return Jsoup.clean(content, "", whitelist, outputSettings);
}
}
2、重写请求参数处理函数,这是实现XSS过滤的关键,在其内重写了getParameter,getParameterValues,getHeader等方法,对http请求内的参数进行了过滤。
package com.example.demo.core.filter;
import org.apache.commons.lang3.StringUtils;
import javax.servlet.http.HttpServletRequest;
import javax.servlet.http.HttpServletRequestWrapper;
/**
* 重写请求参数处理函数
*/
public class XssHttpServletRequestWrapper extends HttpServletRequestWrapper {
HttpServletRequest orgRequest = null;
private boolean isIncludeRichText = false;
public XssHttpServletRequestWrapper(HttpServletRequest request, boolean isIncludeRichText) {
super(request);
orgRequest = request;
this.isIncludeRichText = isIncludeRichText;
}
/**
* 覆盖getParameter方法,将参数名和参数值都做xss过滤.
* 如果需要获得原始的值,则通过super.getParameterValues(name)来获取
* getParameterNames,getParameterValues和getParameterMap也可能需要覆盖
*/
@Override
public String getParameter(String name) {
if (("content".equals(name) || name.endsWith("WithHtml")) && !isIncludeRichText) {
return super.getParameter(name);
}
name = XssFilterUtil.clean(name);
String value = super.getParameter(name);
if (StringUtils.isNotBlank(value)) {
value = XssFilterUtil.clean(value);
}
return value;
}
@Override
public String[] getParameterValues(String name) {
String[] arr = super.getParameterValues(name);
if (arr != null) {
for (int i = 0; i < arr.length; i++) {
arr[i] = XssFilterUtil.clean(arr[i]);
}
}
return arr;
}
/**
* 覆盖getHeader方法,将参数名和参数值都做xss过滤。<br/>
* 如果需要获得原始的值,则通过super.getHeaders(name)来获取<br/>
* getHeaderNames 也可能需要覆盖
*/
@Override
public String getHeader(String name) {
name = XssFilterUtil.clean(name);
String value = super.getHeader(name);
if (StringUtils.isNotBlank(value)) {
value = XssFilterUtil.clean(value);
}
return value;
}
/**
* 获取最原始的request
*
* @return
*/
public HttpServletRequest getOrgRequest() {
return orgRequest;
}
/**
* 获取最原始的request的静态方法
*
* @return
*/
public static HttpServletRequest getOrgRequest(HttpServletRequest req) {
if (req instanceof XssHttpServletRequestWrapper) {
return ((XssHttpServletRequestWrapper) req).getOrgRequest();
}
return req;
}
}
3、添加过滤XSS请求的入口,在这里通过XssHttpServletRequestWrapper将HttpServletRequest进行了封装, filterChain.doFilter(xssRequest, response); 保证了后续代码执行request.getParameter,request.getParameterValues,request.getHeader时调用的都是XssHttpServletRequestWrapper内重写的方法,获取到的参数是已经进行过标签过滤的内容,从而消除了敏感信息。
package com.example.demo.core.filter;
import org.apache.commons.lang3.BooleanUtils;
import org.apache.commons.lang3.StringUtils;
import javax.servlet.*;
import javax.servlet.http.HttpServletRequest;
import javax.servlet.http.HttpServletResponse;
import java.io.IOException;
import java.util.ArrayList;
import java.util.List;
import java.util.regex.Matcher;
import java.util.regex.Pattern;
/**
* @author 张瑶
* @Description: 拦截防止xss注入 通过Jsoup过滤请求参数内的特定字符
* @date 2018/5/16 20:04
*/
public class XssFilter implements Filter {
//是否过滤富文本内容
private static boolean IS_INCLUDE_RICH_TEXT = true;
public List<String> excludes = new ArrayList<>();
@Override
public void doFilter(ServletRequest request, ServletResponse response, FilterChain filterChain) throws IOException, ServletException {
HttpServletRequest req = (HttpServletRequest) request;
HttpServletResponse resp = (HttpServletResponse) response;
if (handleExcludeURL(req, resp)) {
filterChain.doFilter(request, response);
return;
}
XssHttpServletRequestWrapper xssRequest = new XssHttpServletRequestWrapper((HttpServletRequest) request, IS_INCLUDE_RICH_TEXT);
filterChain.doFilter(xssRequest, response);
}
private boolean handleExcludeURL(HttpServletRequest request, HttpServletResponse response) {
if (excludes == null || excludes.isEmpty()) {
return false;
}
String url = request.getServletPath();
for (String pattern : excludes) {
Pattern p = Pattern.compile("^" + pattern);
Matcher m = p.matcher(url);
if (m.find()) {
return true;
}
}
return false;
}
@Override
public void init(FilterConfig filterConfig) throws ServletException {
String isIncludeRichText = filterConfig.getInitParameter("isIncludeRichText");
if (StringUtils.isNotBlank(isIncludeRichText)) {
IS_INCLUDE_RICH_TEXT = BooleanUtils.toBoolean(isIncludeRichText);
}
String temp = filterConfig.getInitParameter("excludes");
if (temp != null) {
String[] url = temp.split(",");
for (int i = 0; url != null && i < url.length; i++) {
excludes.add(url[i]);
}
}
}
@Override
public void destroy() {
}
}
四:注册过滤器
创建core→configurer→XssFilterConfigurer
package com.example.demo.core.configurer;
import com.example.demo.core.filter.XssFilter;
import org.springframework.boot.web.servlet.FilterRegistrationBean;
import org.springframework.context.annotation.Bean;
import org.springframework.context.annotation.Configuration;
import java.util.HashMap;
import java.util.Map;
/**
* @author 张瑶
* @Description:xss过滤拦截器配置文件
* @time 2018/5/16 20:47
*/
@Configuration
public class XssFilterConfigurer {
/**
* xss过滤拦截器
*/
@Bean
public FilterRegistrationBean xssFilterRegistrationBean() {
FilterRegistrationBean filterRegistrationBean = new FilterRegistrationBean();
filterRegistrationBean.setFilter(new XssFilter());
filterRegistrationBean.setOrder(Integer.MAX_VALUE-1);
filterRegistrationBean.setEnabled(true);
filterRegistrationBean.addUrlPatterns("/*");
Map<String, String> initParameters = new HashMap();
//excludes用于配置不需要参数过滤的请求url
initParameters.put("excludes", "/favicon.ico,/img/*,/js/*,/css/*");
//isIncludeRichText主要用于设置富文本内容是否需要过滤
initParameters.put("isIncludeRichText", "true");
filterRegistrationBean.setInitParameters(initParameters);
return filterRegistrationBean;
}
}
五:测试
路径 localhost:8080/userInfo/selectById
请求参数id= 1<a href="http://www.baidu.com/a" onclick="alert("模拟XSS攻击");">sss</a><script>alert(0);</script>sss
结果: 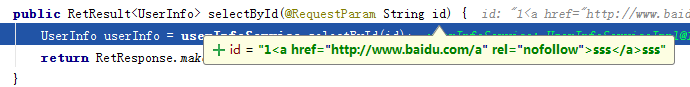
我们可以看到<script></script>已经被过滤掉
项目地址
gitee.com/beany/mySpr…
写文章不易,如对您有帮助,请帮忙点下star 
结尾
添加防止XSS攻击功能已完成,后续功能接下来陆续更新,有问题可以联系我mr_beany@163.com。另求各路大神指点,感谢大家。
- 本文标签: js UI HTML final id web https 配置 App 参数 IO apache map CEO list bean ssh git 安全 代码 value 文章 静态方法 java ip 数据库 漏洞 XSS攻击 http equals spring servlet description CSS Select core ArrayList find IDE Document src HashMap node tar 数据 jsoup example springboot 测试
- 版权声明: 本文为互联网转载文章,出处已在文章中说明(部分除外)。如果侵权,请联系本站长删除,谢谢。
- 本文海报: 生成海报一 生成海报二











![[HBLOG]公众号](https://www.liuhaihua.cn/img/qrcode_gzh.jpg)

